When it comes to your business, secure communication isn’t just a feature—it’s a necessity. Imagine a solution that protects your sensitive data without relying on the internet, keeps your conversations truly private, and adapts to your unique operational needs.
That’s exactly what gettrusted’s new Project Hierophant offers. Designed for mission-critical environments like government, military, and corporate sectors, this cutting-edge system ensures your information stays safe with post-quantum encryption and zero-knowledge protocols. If you’re ready to take your B2B communication to the next level of security and trust, discover how gettrusted can safeguard your business today. Explore the future of secure communication here: gettrusted – Project Hierophant
Introduction To B2b Secure Communication Solutions
B2B secure communication solutions enable businesses to exchange sensitive information safely. These solutions protect data from cyber threats and unauthorized access. Modern companies require robust methods to ensure privacy and trust in their partnerships.
Solutions like Project Hierophant offer advanced, post-quantum secure communication without relying on the internet. This approach suits mission-critical operations in government, military, and corporate sectors.
Understanding B2b Communication Needs And Challenges
B2B communication involves sharing confidential data, contracts, and strategic information. The main challenges include:
- Data privacy: Preventing leaks and unauthorized access.
- Compliance: Meeting legal and industry regulations.
- Complexity: Managing secure communication across multiple platforms.
- Reliability: Ensuring uninterrupted, secure data exchange.
Businesses demand solutions that are easy to use yet highly secure. Many current systems expose metadata or require internet access, increasing risk.
The Role Of Encryption In Building Business Trust
Encryption transforms data into unreadable code for outsiders. It is vital for securing messages and files between companies.
End-to-end encryption (E2E) ensures only the sender and receiver can read the content. This builds trust by guaranteeing confidentiality.
| Encryption Feature | Benefit for B2B |
|---|---|
| Zero Knowledge Architecture | Service providers cannot access data or metadata. |
| Post-Quantum Security | Protection against future quantum computer attacks. |
| No Internet Required | Reduces exposure to online threats and outages. |
Why Secure Communication Is Critical For B2b Relationships
Secure communication is the foundation of strong B2B relationships. It:
- Protects sensitive data like contracts and trade secrets.
- Prevents financial losses from cyberattacks or breaches.
- Meets compliance with data protection laws.
- Supports operational continuity by avoiding disruptions.
- Enhances reputation by showing commitment to security.
Tools like Project Hierophant provide tailored, highly secure communication solutions. Their no-account, zero-metadata design delivers privacy and peace of mind for sensitive business operations.

Credit: globalsolutions.telefonica.com
Key Features Of Top Encryption Solutions For B2b
Top encryption solutions for B2B focus on securing sensitive data and communication. They protect business information from interception, tampering, and unauthorized access. Strong encryption tools build trust between business partners and comply with strict regulations. These solutions combine advanced security features with easy integration for smooth operations.
End-to-end Encryption: Ensuring Confidentiality And Data Integrity
End-to-end encryption (E2EE) locks data from sender to receiver. Only authorized parties can read messages or files. This prevents hackers, service providers, or third parties from seeing the content. E2EE also protects data integrity, ensuring information is not altered during transmission.
For example, Project Hierophant uses E2EE on devices without internet, creating a secure and isolated communication channel. This makes it ideal for sensitive B2B exchanges in defense, government, and corporate sectors.
Authentication Mechanisms: Verifying Business Identities
Authentication confirms the identity of communicating parties. It stops impersonation and unauthorized access. Common methods include digital certificates, multi-factor authentication, and cryptographic keys.
Strong authentication mechanisms build confidence in B2B communications by ensuring messages come from trusted sources only. Project Hierophant employs robust authentication to verify every participant’s identity before data exchange.
Non-repudiation: Guaranteeing Message Authenticity And Accountability
Non-repudiation prevents parties from denying their actions or sent messages. It uses digital signatures and secure logs to prove origin and receipt of data. This feature is critical for legal and compliance reasons in B2B interactions.
With non-repudiation, businesses can track and audit communication history. Project Hierophant’s secure system supports non-repudiation to maintain accountability and trust.
Compliance With Industry Standards And Regulations
Encryption solutions must meet industry rules such as GDPR, HIPAA, or government security standards. Compliance ensures data privacy and avoids legal penalties.
Top solutions like Project Hierophant align with strict regulations by using post-quantum secure protocols and zero-knowledge architecture. They support sector-specific needs in healthcare, finance, defense, and more.
Integration Capabilities With Existing Business Systems
Easy integration allows encryption tools to work with current software and hardware. This reduces disruption and speeds up deployment.
Project Hierophant offers flexible integration options with secure messengers, dedicated hardware, and no-internet infrastructure. It adapts to unique operational and regulatory demands across industries.
| Feature | Benefit | Example from Project Hierophant |
|---|---|---|
| End-to-End Encryption | Protects data confidentiality and integrity | E2EE on devices without internet access |
| Authentication | Verifies trusted business identities | Strong cryptographic identity verification |
| Non-Repudiation | Ensures message authenticity and accountability | Digital signatures and secure logs |
| Compliance | Meets legal and industry standards | Post-quantum security and zero-knowledge protocol |
| Integration | Works with existing systems and workflows | Secure software, hardware, no-internet setup |
Pricing And Affordability Breakdown
Project Hierophant offers a secure communication solution designed for B2B clients with strict security needs. Pricing is structured to fit various business sizes and operational demands. Understanding the costs and options helps businesses plan their investment wisely.
Subscription Models And Licensing Options For B2b Clients
Project Hierophant provides flexible subscription and licensing choices to suit different company requirements. Options include:
- Enterprise Licensing: One-time fee for full software and hardware deployment, ideal for large organizations.
- Annual Subscription: Recurring payments covering software updates, support, and security patches.
- Usage-Based Licensing: Pay according to the number of active users or devices.
Licensing includes access to the proprietary Hierophant protocol, ensuring zero-knowledge, metadata-free secure communication without internet dependency.
Cost-benefit Analysis: Investing In Secure Communication
Investing in Project Hierophant means securing sensitive data with post-quantum encryption. Benefits include:
- Protection against cyber threats and data leaks
- Compliance with strict regulatory and operational standards
- Reduced risk of communication interception
The initial cost may be higher than standard messaging tools, but the value lies in:
- Long-term security assurance
- Lower risk of costly data breaches
- Peace of mind for mission-critical operations
Scalability And Pricing Flexibility For Growing Businesses
Project Hierophant supports scaling from small teams to large enterprises. Pricing adapts to business growth with:
| Business Size | Pricing Model | Key Features |
|---|---|---|
| Small Teams | Subscription (per user) | Basic secure messaging, simple deployment |
| Medium Businesses | Usage-Based Licensing | Enhanced features, flexible user management |
| Large Enterprises | Enterprise Licensing | Full hardware integration, custom solutions |
Flexibility in pricing helps businesses manage budgets without sacrificing security. Upgrades and additional services can be added as needs evolve.
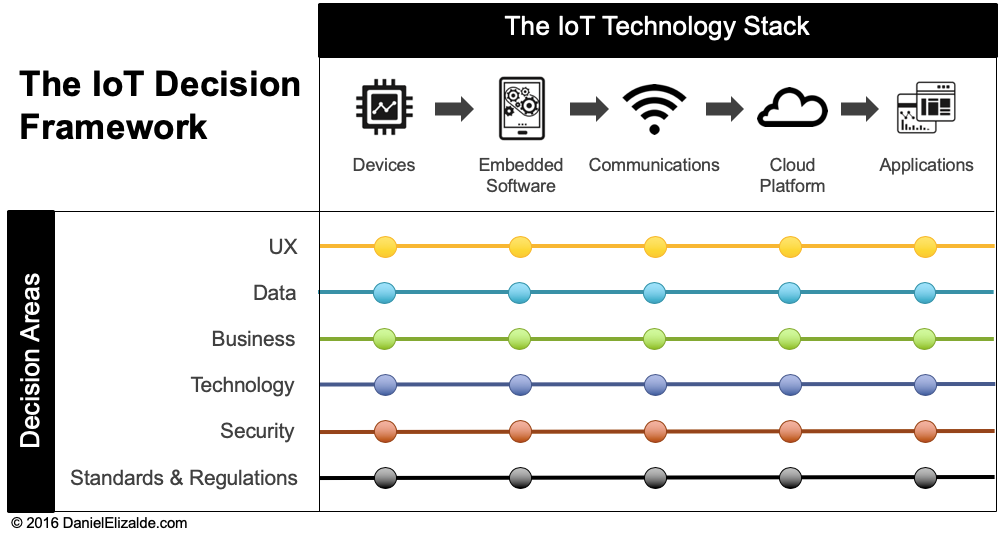
Credit: danielelizalde.com
Pros And Cons Of B2b Secure Communication Solutions
B2B secure communication solutions protect sensitive information exchanged between businesses. These tools offer strong encryption and privacy, ensuring messages and data stay confidential. Understanding the benefits and challenges helps companies decide if such solutions fit their needs.
Advantages: Enhanced Trust, Data Protection, And Business Continuity
Enhanced Trust: Secure communication builds confidence between partners. Businesses feel safe sharing critical data without fear of leaks or spying.
Data Protection: End-to-end encryption and zero-knowledge protocols prevent unauthorized access. Solutions like Project Hierophant use post-quantum security, which guards against future cyber threats.
Business Continuity: These systems operate without internet dependency. This sovereignty ensures communication stays uninterrupted even during network failures or cyber attacks.
- Zero metadata and no account requirements increase privacy.
- Dedicated hardware and OS-free devices reduce hacking risks.
- Protocols adapt to sector-specific rules and operational needs.
Potential Limitations: Implementation Complexity And User Adoption
Implementation Complexity: Installing and configuring advanced secure systems can be difficult. It often needs specialized hardware and training.
User Adoption: Employees may resist new tools that feel complex or unfamiliar. Smooth onboarding and clear instructions are essential to success.
| Challenge | Impact | Solution |
|---|---|---|
| Hardware Setup | Requires investment and expertise | Partner with experienced vendors like gettrusted |
| Training Needs | Slows down adoption | Provide simple guides and support |
| User Resistance | Reduces communication efficiency | Highlight benefits and ease of use |
Real-world Usage Insights And Case Examples
Project Hierophant serves government, military, and mission-critical corporate clients. It supports secure messaging and data exchange without internet reliance.
Clients report improved trust and data safety during sensitive operations. The zero-knowledge design ensures no data leaks, even under heavy surveillance.
- Government Agencies: Use the system for classified communications with total privacy.
- SCADA Operators: Maintain control over industrial networks amid cyber threats.
- Corporate Teams: Secure high-value contracts and intellectual property exchange.
These examples show how B2B secure communication solutions protect vital information and help maintain continuous operations under pressure.
Recommendations For Ideal Users And Use Cases
gettrusted’s Project Hierophant fits organizations needing highly secure communication. Its unique protocol supports sensitive data exchange without internet use. This section outlines who benefits most from this solution and the scenarios it suits best.
Businesses Handling Sensitive Information And Intellectual Property
Companies managing confidential data or intellectual property require robust protection. Project Hierophant offers:
- End-to-end encryption ensuring data stays private on devices only.
- Zero knowledge architecture that prevents data exposure, even to providers.
- No metadata or accounts to eliminate tracking risks.
Industries like legal, R&D, and finance gain strong defense against leaks and cyber threats.
Enterprises Seeking Compliance With Regulatory Requirements
Regulated sectors face strict rules on data privacy and secure communication.
Project Hierophant supports compliance by:
- Operating with a post-quantum secure protocol for future-proof protection.
- Providing a no-internet infrastructure option, reducing external risks.
- Ensuring sector-specific configurations to meet unique legal demands.
Healthcare, government, and defense organizations benefit from aligning with regulations effortlessly.
Organizations Focusing On Long-term Partnerships And Trust Building
Trust is key in lasting B2B relationships. Secure communication fosters transparency and confidence.
gettrusted enables:
- Confidential exchanges without third-party interference.
- Clear, secure channels that protect reputations.
- Commitment to privacy that builds partner loyalty.
Businesses aiming for reliable, long-term connections find this solution ideal.
Scenarios Benefiting From Seamless Integration And Scalability
Growing enterprises need solutions that fit existing systems and scale smoothly.
| Feature | Benefit |
|---|---|
| Proprietary Protocol Hierophant | Customizable for diverse operational needs. |
| Dedicated Hardware & Software | Easy deployment on various infrastructures. |
| No Internet Required | Works in isolated or secure environments. |
| Zero-Knowledge Architecture | Maintains privacy as client base grows. |
Enterprises with complex workflows and expansion plans benefit from this flexible, scalable solution.

Credit: news.samsung.com
Frequently Asked Questions
What Is B2b In Communication?
B2B communication involves exchanging information and marketing between businesses. It builds relationships, solves problems, and supports sales. It targets key decision-makers using digital and traditional channels. Content focuses on value and solutions to foster trust and long-term partnerships.
What Is B2b Encryption?
B2B encryption secures data exchanged between businesses to protect sensitive information. It ensures confidentiality, integrity, and trust during communication and transactions.
What Is A B2b Solution?
A B2B solution is a product or service designed to help businesses improve operations, efficiency, and sales. It targets companies, not consumers, and focuses on solving specific business challenges. These solutions often include software, consulting, or platforms that streamline processes and foster growth.
What Are The Four Elements Of Secure Communication?
The four elements of secure communication are confidentiality, integrity, authentication, and non-repudiation. These ensure data privacy, accuracy, verified identities, and accountability during information exchange.
Conclusion
Secure communication protects your business data and builds trust. Project Hierophant offers strong encryption without internet use. It ensures zero knowledge and no metadata exposure. This solution fits mission-critical and regulated industries well. Using gettrusted enhances your company’s safety and efficiency. Explore how Project Hierophant can meet your secure communication needs. Learn more about this new solution at gettrusted. Take steps today to keep your communications safe and private.





